AWS CloudTrail provides audit trail for your cloud infrastructure. This is one of the services that should be enabled by default, but it’s not. Enabling AWS CloudTrail on all your AWS accounts is good security practice. nOps Rule allows you to monitor AWS CloudTrail across regions and projects. You receive real-time notification if AWS CloudTrail is disabled.
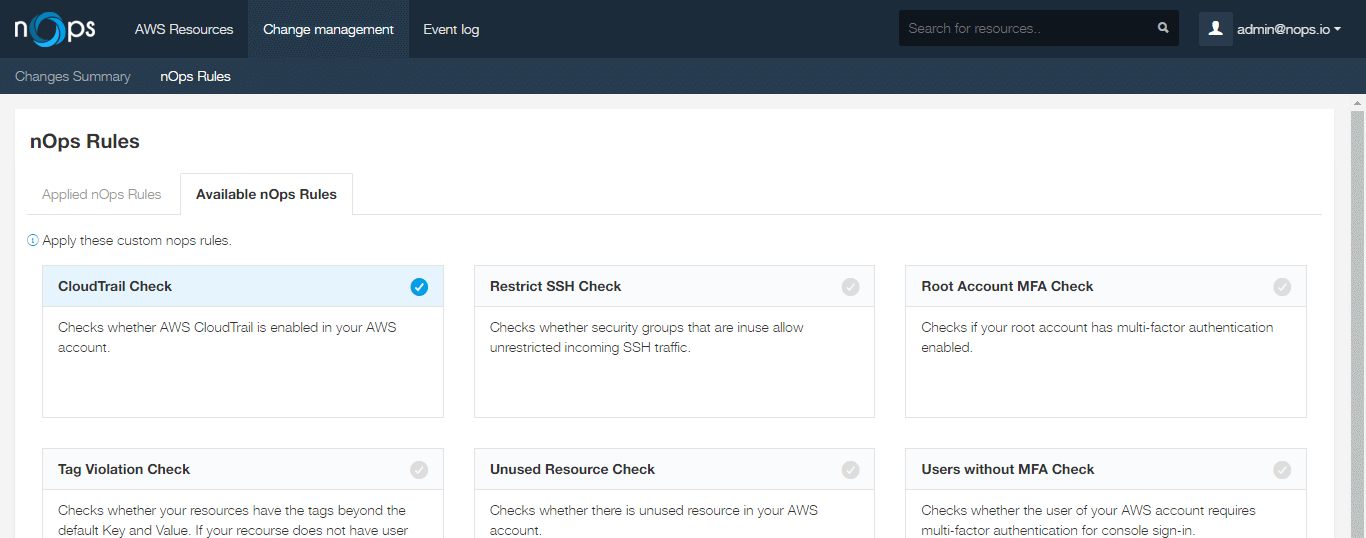
AWS CloudTrail Rule
To enable the rule, simply go to the “Available nOps Rules” tab in nOps Rules and click on the “CloudTrail Check” rule.
AWS CloudTrail Summary
Once enabled, the rule will appear on the “Applied nOps Rules” tab with a summary of all resources that violates the rule.
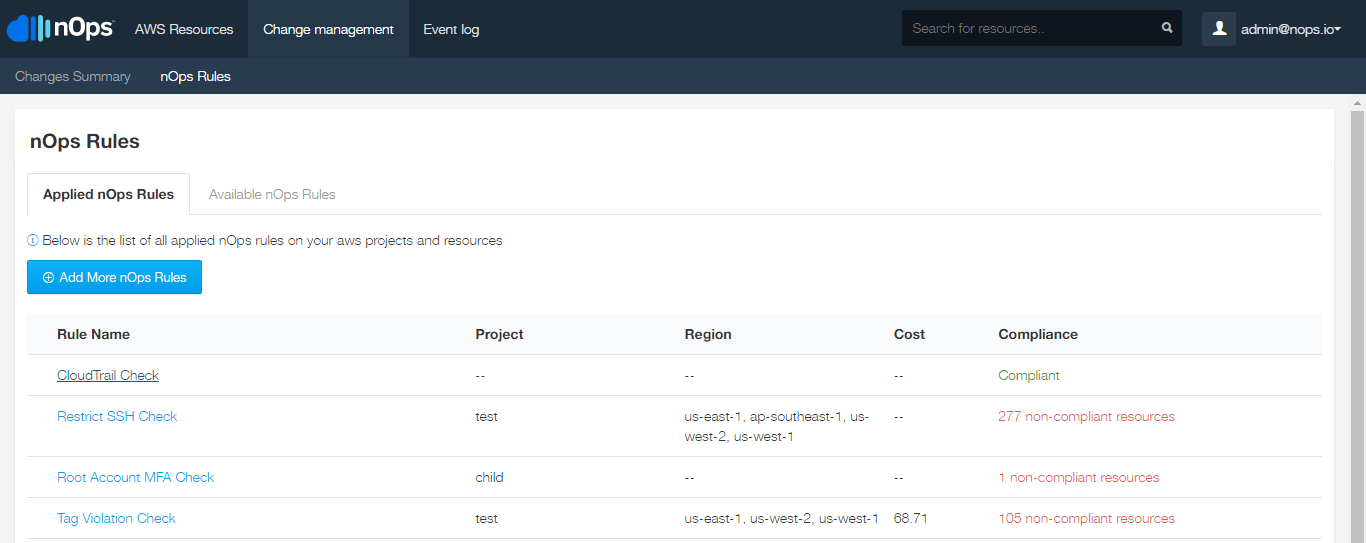
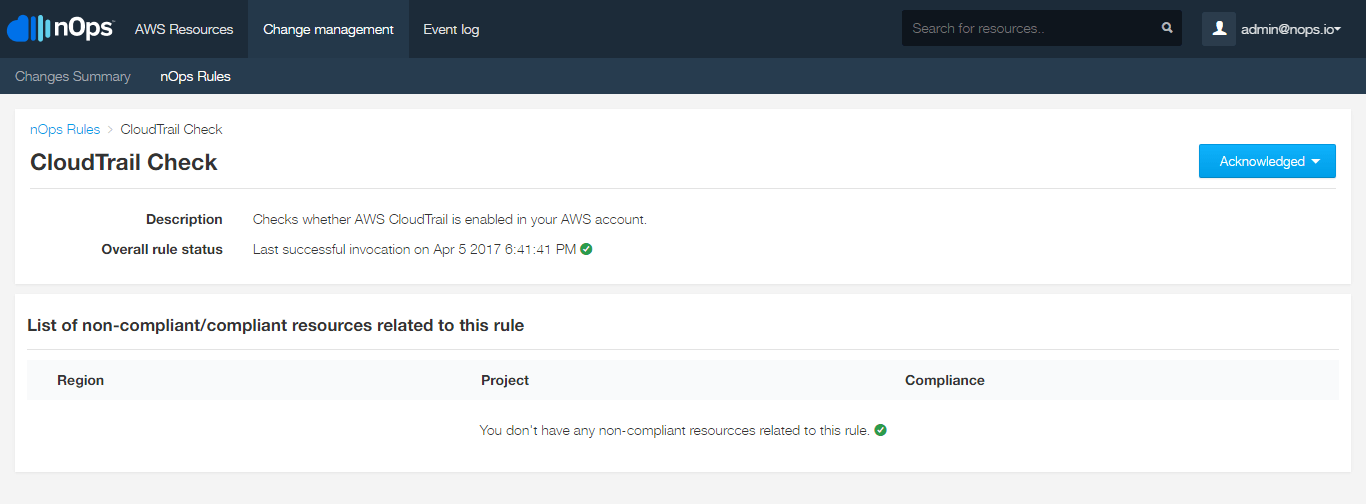
AWS CloudTrail Detail
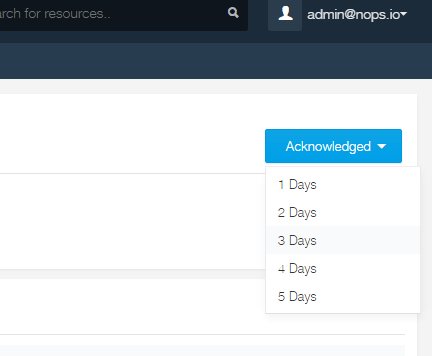
Clicking on the rule in the “Applied nOps Rules” tab, you will be able to see, in detail, the when this check was performed.
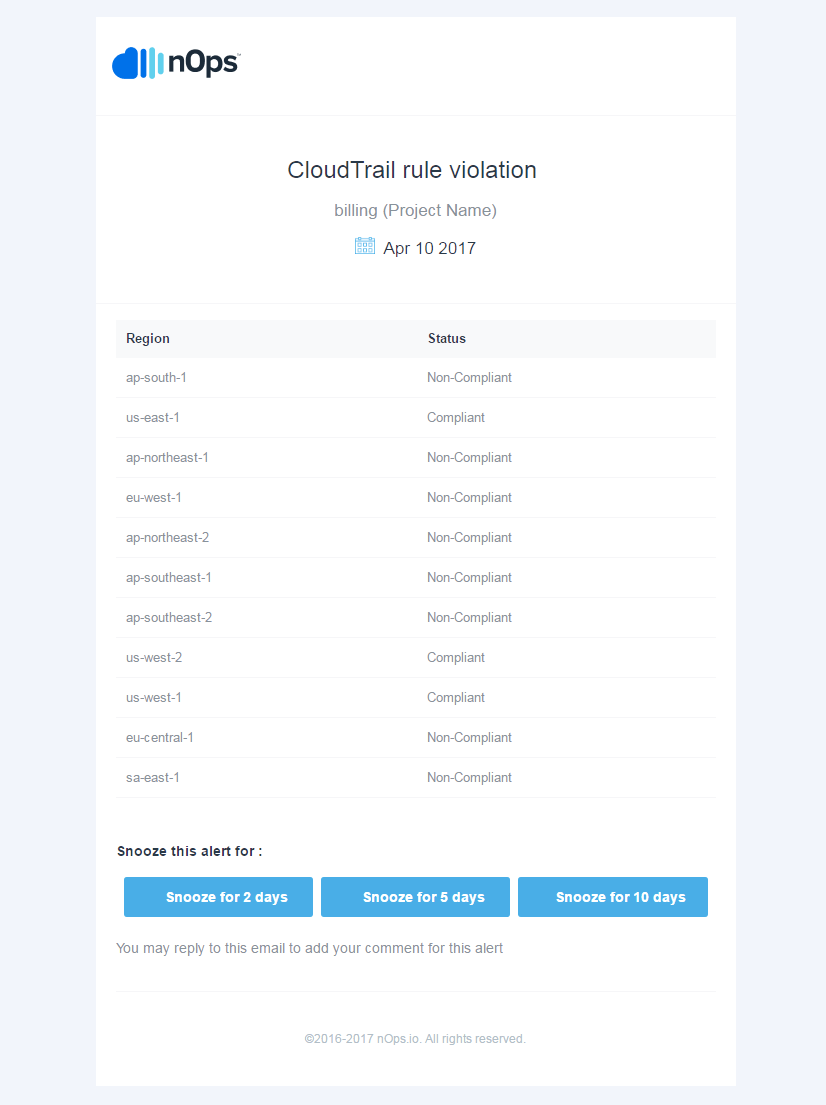
AWS CloudTrail Alerts
Once enabled, you can configure your nOps account to receive email, Slack, and/or Hipchat alerts, alerting you to when Cloudtrail is enable or disable on the AWS console.