Upcoming Event nOps at FinOps X 2026 - Register to Join
Upcoming Event nOps at FinOps X 2026 - Register to Join
Ensure that Multi-Factor Authentication (MFA) is enabled for your root account in order to secure your AWS environment and adhere to IAM security best practices.
This rule can help you with the following compliance standards:
This rule can help you work with the AWS Well-Architected Framework
Having an MFA-protected root account is the best way to protect your AWS resources and services against attackers. An MFA device signature adds an extra layer of protection on top of your existing root credentials making your AWS root account virtually impossible to penetrate without the MFA generated passcode.
To determine if your AWS root account is MFA-protected, perform the following:
1. Sign in to the AWS Management Console using your root credentials.
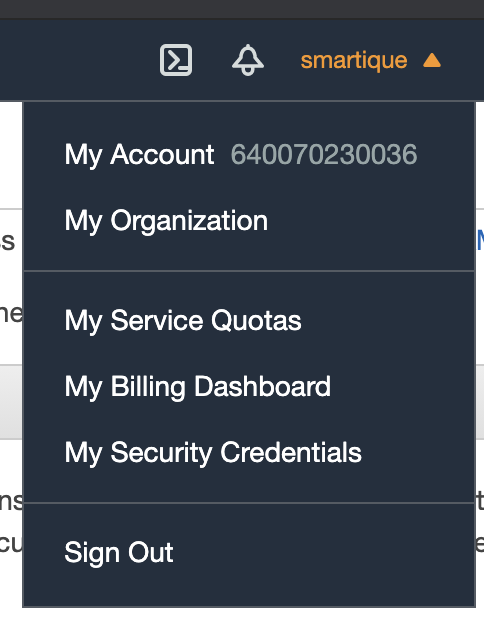
2. Click on the AWS account name or number in the upper-right corner of the management console and select Security Credentials from the dropdown menu:
3. Expand the Multi-Factor Authentication (MFA) section.
4. Inside the MFA management section, check for any enabled MFA devices e.g.
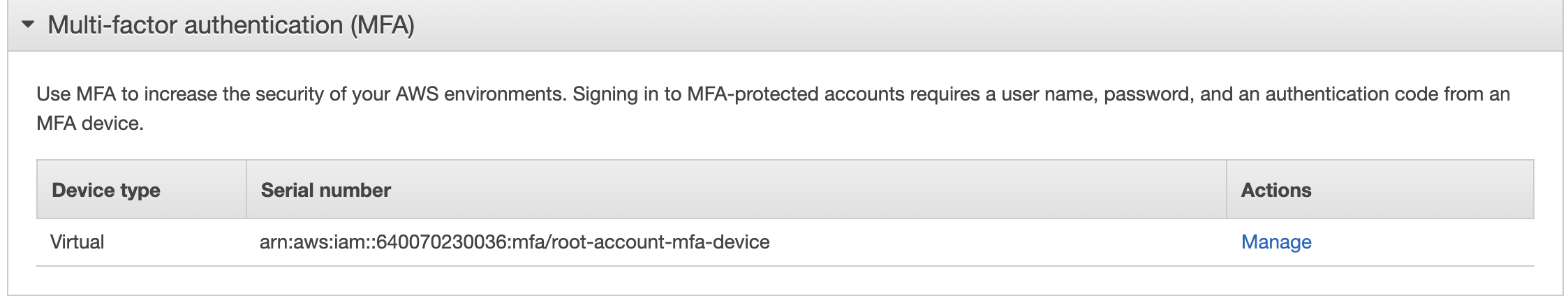
5. If there are no MFA devices listed and the Activate MFA button is displayed, your root account is not MFA-protected and the authentication process is not following AWS IAM security best practices.
6. Repeat steps no. 1 – 4 for each AWS root account that you want to examine.
1. Run get-account-summary command (OSX/Linux/UNIX) to obtain the infotmation about your AWS Account.
aws iam get-account-summary
2. The command output should display the SummaryMap containing the general information about your AWS Account as follows:
{ "SummaryMap": { "GroupPolicySizeQuota": 5120, "InstanceProfilesQuota": 1000, "Policies": 0, "GroupsPerUserQuota": 10, "InstanceProfiles": 0, "AttachedPoliciesPerUserQuota": 10, "Users": 1, "PoliciesQuota": 1500, "Providers": 0, **"AccountMFAEnabled": 1,** "AccessKeysPerUserQuota": 2, "AssumeRolePolicySizeQuota": 2048, "PolicyVersionsInUseQuota": 10000, "GlobalEndpointTokenVersion": 1, "VersionsPerPolicyQuota": 5, "AttachedPoliciesPerGroupQuota": 10, "PolicySizeQuota": 6144, "Groups": 0, "AccountSigningCertificatesPresent": 0, "UsersQuota": 5000, "ServerCertificatesQuota": 20, "MFADevices": 1, "UserPolicySizeQuota": 2048, "PolicyVersionsInUse": 3, "ServerCertificates": 0, "Roles": 2, "RolesQuota": 1000, "SigningCertificatesPerUserQuota": 2, "MFADevicesInUse": 1, "RolePolicySizeQuota": 10240, "AttachedPoliciesPerRoleQuota": 10, "AccountAccessKeysPresent": 0, "GroupsQuota": 300 } }
3. Look for the value of AccountMFAEnabled in the output. A value of 1 shows that the MFA is enabled on the root account.
4. Repeat steps no. 1 – 4 for each AWS root account that you want to examine via CLI.
To enable MFA access protection for your AWS root account, perform the following:
As example, this guide will use Google Authenticator as MFA device since this is one of the most popular MFA virtual applications used by AWS customers. To explore other MFA devices (virtual and hardware) and their features please visit http://aws.amazon.com/iam/details/mfa/
1. Sign in to the AWS Management Console using your root credentials.
2. Click on the AWS account name or number in the upper-right corner of the management console and select Security Credentials from the dropdown menu:
3. On Your Security Credentials page, click on the Multi-Factor Authentication (MFA) accordion tab to expand the MFA management section.
4. In the MFA management section click the Activate MFA button to initiate the MFA device setup.
5. In the Manage MFA Device dialog box, select A virtual MFA device and click Next Step.
6. Now install the AWS MFA-compatible application. The MFA application used in this example is Google Authenticator. This guide assumes that you have already the application installed on your smartphone at this point, otherwise just follow these simple steps: https://goo.gl/cvl2Y. Once the application is installed, click Next Step.
7. Click on Show QR code and then scan it using the Google Authenticator application.
8. Enter two consecutive authentication passcodes in the Authentication Code 1 and Authentication Code 2 boxes, then click Activate Virtual MFA to complete the MFA device setup process.
a. If successful, the following message will be displayed:
The MFA device was successfully associated
b. Click Finish to exit the setup wizard.
The new MFA virtual device should be listed inside the Multi-Factor Authentication (MFA) section.
9. Repeat steps no. 1 – 8 for each AWS root account that you want to protect using an MFA device.
Installing and activating an MFA device for the AWS root account via Command Line Interface (CLI) is not currently supported.