Upcoming Event Austin FinOps Executive Dinner - Register to Join
Identify and remove any unused NAT Gateways to adhere to best practices and avoid unnecessary costs. NAT gateways are used to connect a private instance with outside networks. When a NAT gateway is provisioned, AWS charges you based on the number of hours it was available and the data (GB) it processes.
This rule can help you with the following:
Compliance Frameworks
AWS Well-Architected Lens
CloudWatch, AWS monitoring service can be used monitor your NAT gateway via information it collects from the specified NAT gateway. This information is collected and presented in readable metrics at 1 minute intervals and are stored for 15 months. nOps uses one such metric to determine if a NAT Gateway is considered unused or not. This metric is BytesOutToDestination which is The number of bytes sent out through the NAT gateway to the destination.
A NAT gateway is considered unused if the value of BytesOutToDestination is 0 for the last 7 days.
1. Sign in to the AWS Management Console.
2. Navigate to the VPC dashboard at https://console.aws.amazon.com/vpc/.
3. In the left navigation panel, under the Virtual Private Cloud section, choose NAT Gateways
4. Click on the NAT Gateway Id that you want to examine to expand the details.
5. Scroll down to the Monitoring section and perform the following actions:
a. Expand Bytes out to destination (Bytes)usage graph thumbnail to open the NAT Gateway outbound usage details box.
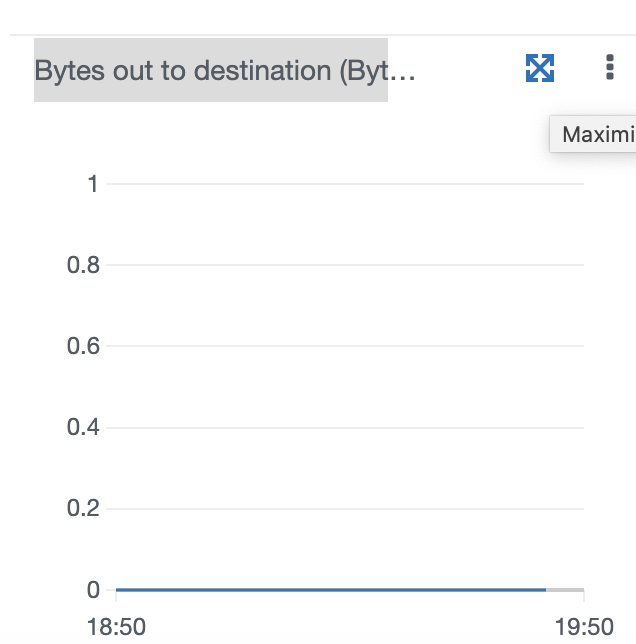
Inside the CloudWatch Monitoring Details dialog box set the following parameters:
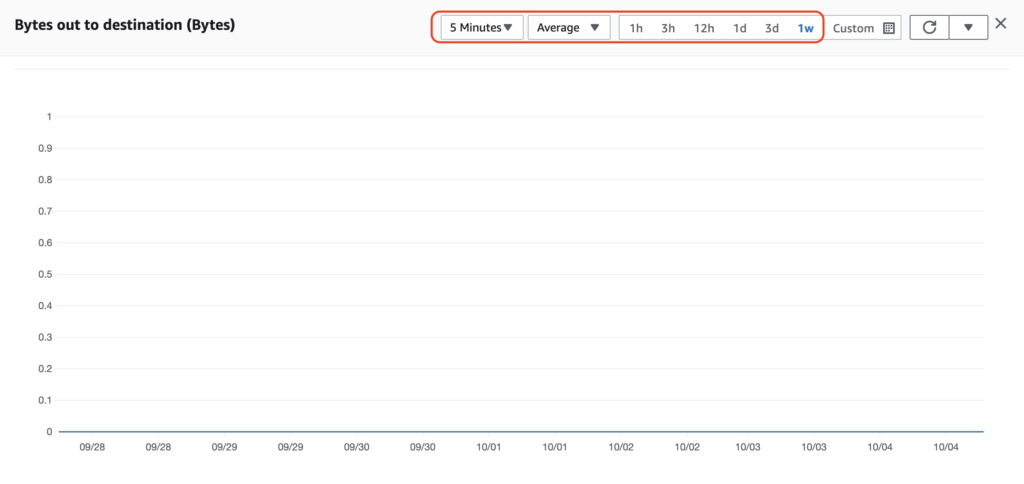
Once the monitoring data is loaded, verify the NAT Gateway Bytes out to destination (Bytes) usage for the last 7 days. If the average usage (bytes) has been 0 for the previous 7 days, then the NAT Gateway in question qualifies as unused and should be deleted to save unnecessary costs. For Example, the above selected NAT Gateway qualifies as such a candidate.
6. To determine the usage for the rest of the NAT gateway provisioned in the current region, repeat steps 4 and 5.
7. To verify that of other AWS regions, use the navigation bar to change the current AWS region and apply the audit process as specified in the previous steps.
describe-nat-gateways command (OSX/Linux/UNIX) using appropriate filtering to list the IDs of all the existing NAT Gateway Ids available in the selected region: aws ec2 describe-nat-gateways \\ --region us-east-1 \\ --query 'NatGateways[*].NatGatewayAddresses[*].NetworkInterfaceId'
2. The command output should return a table with the requested NAT Gateway IDs:
------------------------- | NetworkInterfaceId | +-----------------------+ | nat-0755b0648c536bcf6 | | nat-03759800f8178b12c | | nat-0fb6cec931e056901 | | nat-0fbc27bc734d0612b | | nat-01f908909e041daf4 | | nat-063fa6307255cbfea |
3. Run get-metric-statistics command (OSX/Linux/UNIX) to get the statistics recorded by AWS CloudWatch for the BytesOutToDestination metric representing the selected NAT Gateway resource usage.
a. Change the –start-time (start recording date) and –end-time (stop recording date) parameters value to choose your own time frame for recording the NAT Gateway usage.
b. Set the –period parameter value based on your requirements to define the granularity – in seconreturned data points’ granularity in secondsata points. A period can be as short as five minutes (300 seconds) or as long as one day (86400 seconds).
The following command example returns the BytesOutToDestination of a NAT gateway by the ID ****nat-0755b0648c536bcf6, usage data captured during a 7 days period (set by the –start-time and –end-time command parameters), using 5 minutes period as the granularity of the returned data points (set by the –period parameter):
aws cloudwatch get-metric-statistics \\ --region us-east-1 \\ --metric-name BytesOutToDestination \\ --start-time 2021-07-31T22:30:00 \\ --end-time 2021-08-06T22:30:00 \\ --period 3600 \\ --namespace AWS/NATGateway \\ --statistics Average \\ --dimensions Name=InstanceId,Value=**nat-0755b0648c536bcf6**
{ "Label": "BytesOutToDestination", "Datapoints": [] } 5. If there are no Datapoints for the last seven days, then the NAT Gateway resource is considered unused and can be safely deleted.
6. Repeat steps no. 3 – 4 to verify the usage of other NAT Gateway resources provisioned in the current region.
7. To verify that of other AWS regions, change the AWS region by updating the --region command parameter value and and apply the audit process as specified in the previous steps.
You should consider deleting any AWS NAT Gateway you no longer need a NAT gateway.
Upon deletion, a NAT Gateway’s entry remains visible for about an hour in the VPC console. After this specified time elapses, the entry is automatically removed. Note that you can’t remove this entry yourself.
Deleting a NAT gateway disassociates its Elastic IP address but does not release the address from your account. If you delete a NAT gateway, the NAT gateway routes remain in a blackhole status until you delete or update the routes.
To delete any NAT Resource that is currently unused, perform the following commands:
1. Sign in to the AWS Management Console.
2. Navigate to the VPC dashboard at https://console.aws.amazon.com/vpc/.
3. In the left navigation panel, under the Virtual Private Cloud section, choose NAT Gateways
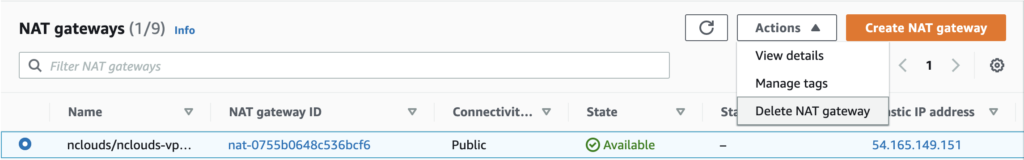
4. Select the radio button for the NAT gateway you want to delete (see the Audit section above to determine which ones you want to delete).
5. Choose Actions from the top right dropdown and click on Delete NAT gateway.
delete and then choose Delete. 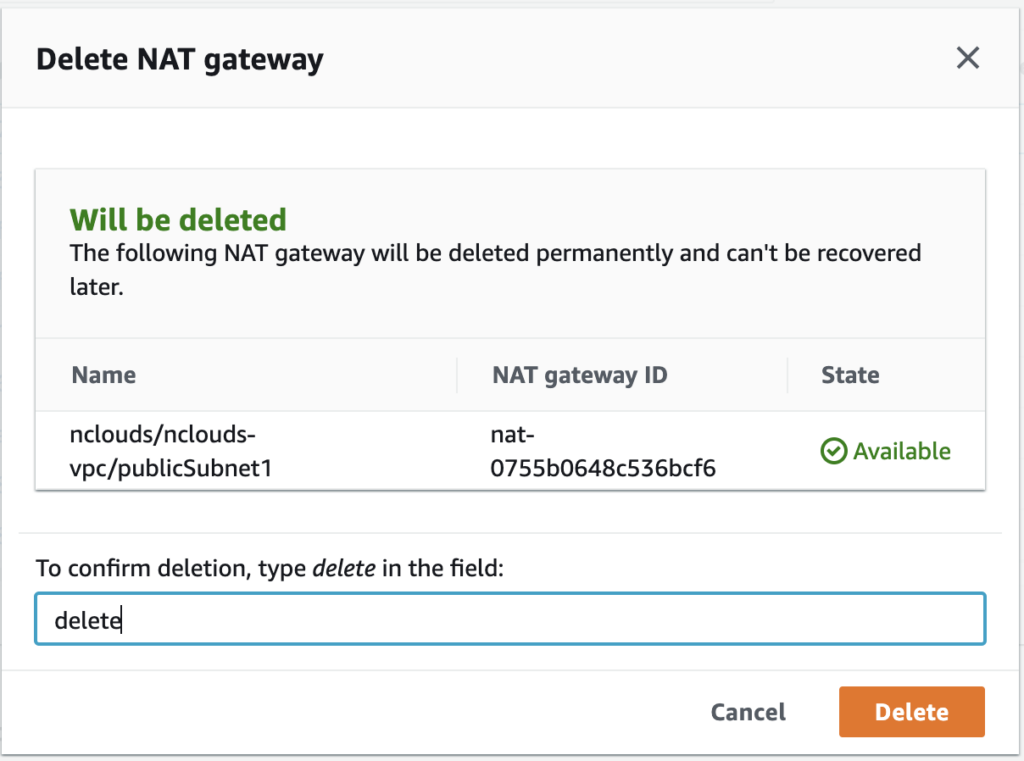
7. If you no longer need the Elastic IP address associated with a public NAT gateway, we recommend that you release it. For more information, see EC2-001 Unused Elastic IP Addresses
8. Repeat Steps 4 -7 for any other NAT Gateway resource you want to delete in the current region.
9. Change the AWS region from the navigation bar and repeat steps 4 – 7 to remove any unused NAT Gateway resource within the other regions.
1. Run describe-nat-gateways command (OSX/Linux/UNIX) using appropriate filtering to list the IDs of all the existing NAT Gateway Ids available in the selected region:
aws ec2 describe-nat-gateways \\ --region us-east-1 \\ --query 'NatGateways[*].NatGatewayAddresses[*].NetworkInterfaceId'
2. The command output should return a table with the requested NAT Gateway IDs:
------------------------- | NetworkInterfaceId | +-----------------------+ | nat-0755b0648c536bcf6 | | nat-03759800f8178b12c | | nat-0fb6cec931e056901 | | nat-0fbc27bc734d0612b | | nat-01f908909e041daf4 | | nat-063fa6307255cbfea |
3. Run delete-nat-gateway command using the NetworkInterfaceId as the Identifier to delete any NAT Gateway in the current region:
aws ec2 delete-nat-gateway \\ –-region us-east-1 \\ --nat-gateway-id nat-0755b0648c536bcf6
4. The command output should return the NAT Gateway ID if the deletion is successful.
{ "NatGatewayId": "nat-0755b0648c536bcf6" } 5. If you want to release (remove) the ElasticIP address associated with the deleted NAT Gateway, please refer to EC2-001 Unused Elastic IP Addresses
6. Repeat step no. 3 to delete any other unused NAT Gateway available in the selected region.
7. Repeat steps no. 1 – 3 to delete any unused NAT Gateway available in different AWS regions.