Upcoming Event nOps at FinOps X 2026 - Register to Join
Upcoming Event nOps at FinOps X 2026 - Register to Join
Validated AWS CloudTrail log files are essential in security and forensic investigations. This rule checks and lists AWS accounts that don’t have the CloudTrail bucket protected from deletion or overwrite.
When you activate the log file integrity validation option, CloudTrail will generate a hash using industry-standard algorithms for each log file that it delivers to your specified S3 bucket.
This rule can help you with the following:
1. Access the CloudTrail dashboard at https://console.aws.amazon.com/cloudtrail/.
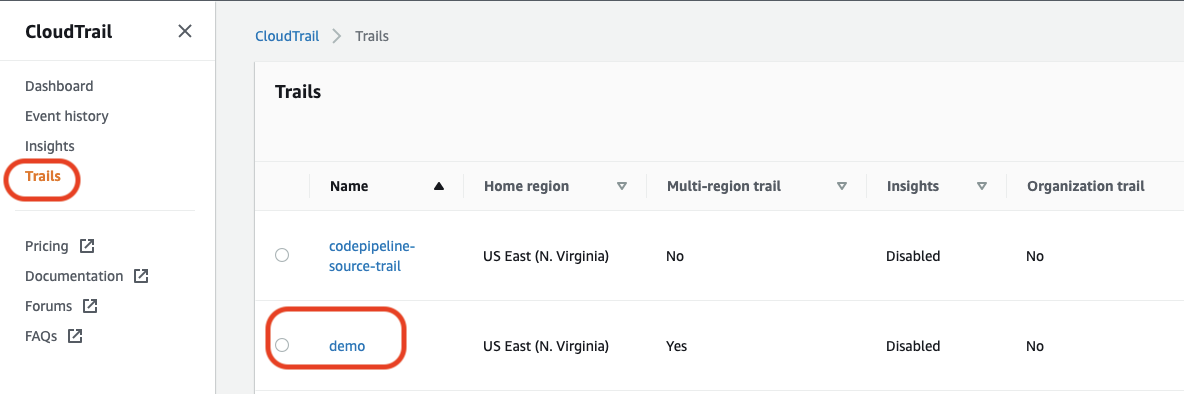
2. Click the CloudTrail left navigation panel and select the Trails option.
3. You should see all the trails that you have created in your AWS account for this region.
4. Choose the trail name that you would like to inspect its properties.
For Example, we will be looking at the demo multi-region trail that we have configured for Management Events in our AWS account.
5. Check the value stated under the Log file validation under the General Details section.
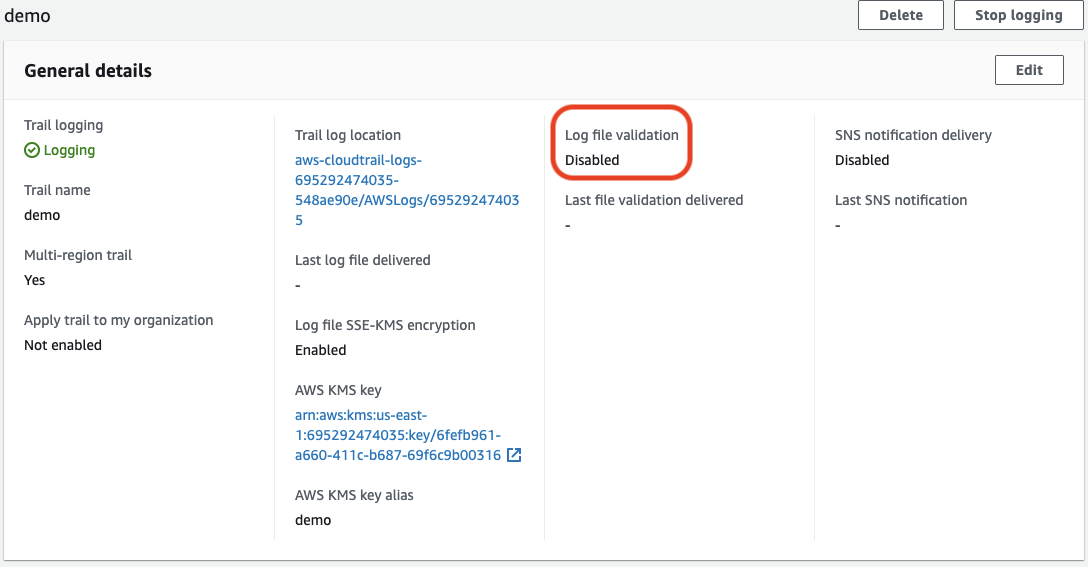
If the feature status is set to Disabled (as shown in the above screenshot), log file integrity validation is not enabled for the trail in question.
1. Execute the describe-trails command to retrieve the list of all trails available in the selected AWS region.
aws cloudtrail describe-trails \\ --region us-east-1
2. The resulting output will display the properties for all configured trails in the region as shown below:
{ "trailList": [ ... { "Name": "demo", "S3BucketName": "aws-cloudtrail-logs-695292474035-548ae90e", "IncludeGlobalServiceEvents": true, "IsMultiRegionTrail": true, "HomeRegion": "us-east-1", "TrailARN": "arn:aws:cloudtrail:us-east-1:695292474035:trail/demo", **"LogFileValidationEnabled": false,** "KmsKeyId": "arn:aws:kms:us-east-1:695292474035:key/6fefb961-a660-411c-b687-69f6c9b00316", "HasCustomEventSelectors": false, "HasInsightSelectors": false, "IsOrganizationTrail": false } ... ] } Check for the LogFileValidationEnabled parameter for the Trail that you are examining. If it is set to false, then the Log File Integrity Check is disabled for this Trail.
3. Repeat steps no. 1 – 2 for each Trail available in the current region. To check for other trails in other regions, switch the AWS region from the top navigation bar and repeat the entire process.
1. Access the CloudTrail dashboard at https://console.aws.amazon.com/cloudtrail/.
2. Click the CloudTrail left navigation panel and select the Trails option.
3. Choose the trail name that you would like to inspect its properties and update its status.
4. Click on the Name of the Trail to examine its properties.
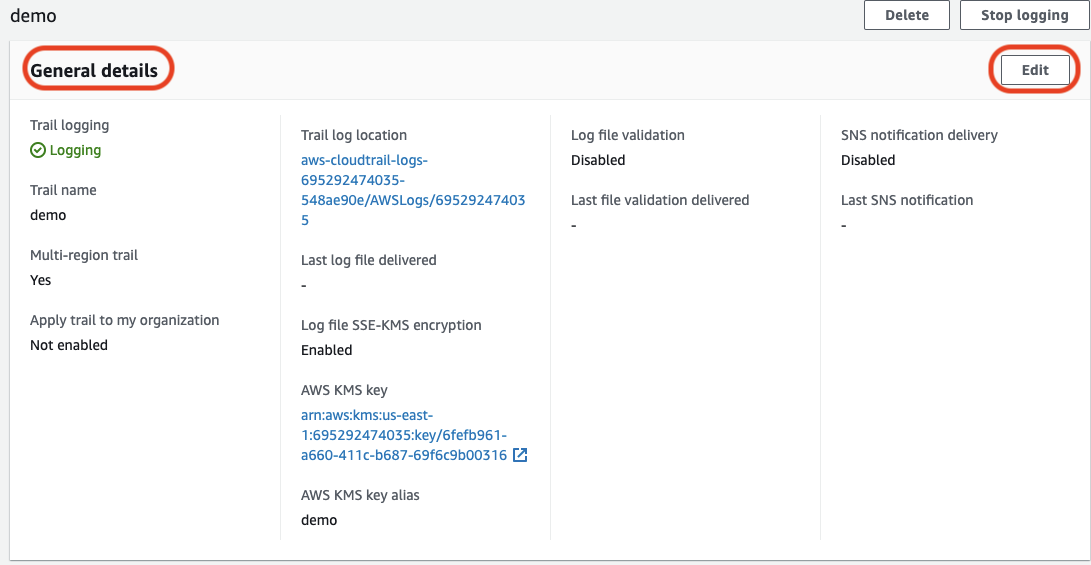
5. Under the General Details section, click on Edit to update the properties
6. Scroll down to the Additional Settings sub-section and check the Enabled box for the Log file validation property.
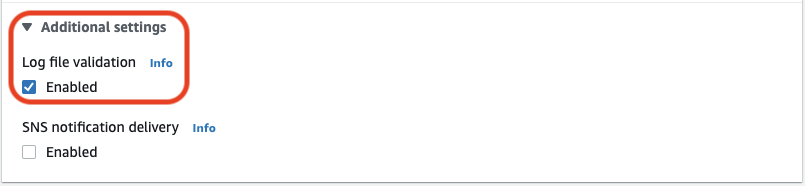
7.Save Changes
8. Repeat Steps 3 – 7 for any other trail available in the current region.
9. To update the Log File Integrity Checks for other trails in other regions, switch the AWS region from the top navigation bar and repeat the entire process.
1. Execute the describe-trails command to retrieve the list of all trails in the specified AWS region.
aws cloudtrail describe-trails \\ --region us-east-1
2. The resulting output will display the properties for all configured trails in the region as shown below:
{ "trailList": [ ... { "Name": "demo", "S3BucketName": "aws-cloudtrail-logs-695292474035-548ae90e", "IncludeGlobalServiceEvents": true, "IsMultiRegionTrail": true, "HomeRegion": "us-east-1", "TrailARN": "arn:aws:cloudtrail:us-east-1:695292474035:trail/demo", **"LogFileValidationEnabled": false,** "KmsKeyId": "arn:aws:kms:us-east-1:695292474035:key/6fefb961-a660-411c-b687-69f6c9b00316", "HasCustomEventSelectors": false, "HasInsightSelectors": false, "IsOrganizationTrail": false } ... ] } Check for the LogFileValidationEnabled parameter for the Trail that you are examining. If it is set to false, then the Log File Integrity Check is disabled for this Trail.
3. Execute the update-trail command along with the trail-name option to update the configuration and activate the flag. A sample of such command is shown below.
aws cloudtrail update-trail \\ --region us-east-1 \\ --name demo \\ --enable-log-file-validation **Output** { "Name": "demo", "S3BucketName": "aws-cloudtrail-logs-695292474035-548ae90e", "IncludeGlobalServiceEvents": true, "IsMultiRegionTrail": true, "TrailARN": "arn:aws:cloudtrail:us-east-1:695292474035:trail/demo", **"LogFileValidationEnabled": true,** "KmsKeyId": "arn:aws:kms:us-east-1:695292474035:key/6fefb961-a660-411c-b687-69f6c9b00316", "IsOrganizationTrail": false }
4. Repeat step 3 for all the available trails in your current region you intended to update their log file integrity validation status by modifying the --name attribute.
5. Modify the --region attribute in the query above to switch to other AWS regions. After that, repeat the entire remediation process to activate the log file integrity validation feature.