- Blog
- AWS Compliance
- How the AWS Well-Architected Tool Helps Improve Security
How the AWS Well-Architected Tool Helps Improve Security
Last Updated: February 1, 2024, AWS Compliance
Cloud security is of the essence, especially at a time when cyber threats are becoming overly sophisticated and detrimental. Data breaches, malware, phishing, and denial-of-service attacks have become common issues. Also, with misconfigurations rife, most organizations miss out on crucial security aspects, leading to widespread breaches.
The AWS Well-Architected Tool provides AWS partners with a consistent approach to review their workloads against AWS best practices. It also guides you on how to design workloads for the cloud. The Well-Architected Framework helps you build and deploy faster and mitigate risks.
How Does the AWS Well-Architected Tool Enhance Organizational Security?
Security in AWS is a shared responsibility between you and AWS. AWS is responsible for the security of the cloud. This means it protects the infrastructure that runs AWS services. It is your responsibility to provide security in the cloud. This includes application security, access management, encryption, and much more.
The AWS Well-Architected Tool helps you to meet security objectives in the following ways:
Infrastructure Security
The AWS Well-Architected Tool helps you keep up to date with security threats and vulnerabilities. It allows you to identify and prioritize risks using a threat model.
Protecting your infrastructure involves various elements, such as layered architecture and defense in depth. With this tool, you can enforce boundary protection, monitoring, and alerts as part of your security plan.
Ideally, it helps you map out a process for responding to security incidents. You can easily monitor your workloads and get real-time insights into your threat environment. With knowledge of the threats and vulnerabilities that your business faces, it is easy to implement security strategies.
Data Protection
It is crucial to protect data from unauthorized access or use. The AWS Well-Architected Tool allows you to classify data depending on its sensitivity. You can encrypt critical data as well, rendering it unintelligible to unauthorized users.
Data classification helps in the following ways:
- It identifies your data.
- It sets protection controls.
- It defines data life cycles.
Proper classification forms the basis of a successful data protection plan.
Identity and Access Management (IAM)
IAM is crucial in the security program as it ensures only authorized users can access certain resources. The IAM service for the AWS Well-Architected Tool helps to securely control all AWS resources. It makes it easier to create, manage, and revoke access to your critical systems. This tool makes it simple to encrypt data, manage keys, and automate key rotation.
Logging
The AWS Well-Architected Tool logs and monitors system activities, making it easy to detect threats in real time. It provides all reports in a central dashboard, so you can leverage them and make decisions. This tool also monitors application usage and unusual or unauthorized activities. In case the tool detects anything unusual, it sends automatic alarms to notify management personnel.
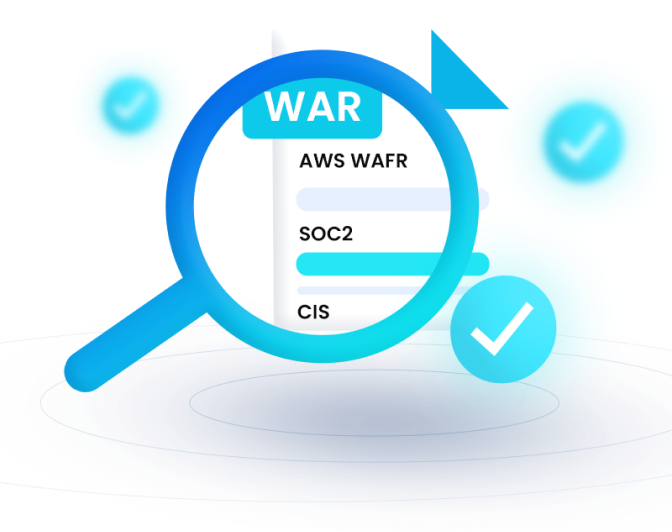
Helps with Compliance
The AWS Well-Architected Tool allows you to identify any compliance gaps in your IT environment. With more profound insights into your compliance gaps, it is easier to remediate and stay in line with the regulations.
Map Out Your AWS Infrastructure with nOps AWS Well-Architected Tool
Achieving cloud security can be challenging. However, the design of the AWS Well-Architected Tool is to help organizations build secure workloads.
Through integration with the AWS Well-Architected Tool, nOps allows you to visualize your cloud environment to identify the areas that need improvement. This helps all users to understand their various roles and responsibilities. Also, this integration allows for continuous monitoring and real-time detection of threats.
Start your free trial today and see how we can improve your AWS security posture!
Looking for more security and compliance help? Check out the AWS Guide to Security and Compliance.