SOC 2 Mapping: Breaking Down the Five Trust Principles
SOC 2 Mapping, also known as Service Organization Controls Type 2, helps companies obtain, transmit, and control data using acceptable methods. Being SOC 2 compliant helps companies experience two major benefits. First, you build trust with new and potential customers. And second, you get a competitive edge in security.
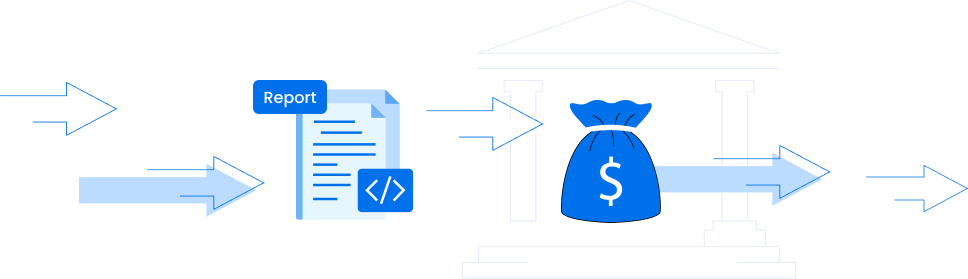
A company has to go through an audit. From the audit, it’ll receive a SOC 2 report proving the organization can process a customer’s data properly. There have been many other data protection laws, such as GDPR. But what makes SOC 2 Mapping unique?
SOC 2 spans over a longer period, hence capturing how the company handles data in different market environments.
- It’s ideal for both large and small companies. It teaches best practices on handling large amounts of data and critical information.
- SOC 2 Mapping integrates protocols from both SOC 1 and COSO frameworks. For this reason, most security risks decline.
A Breakdown of the Five SOC 2 Mapping Principles
Principal 1 — Security:
This trust principle ensures the security of both the provider and the consumer of IT services. It ensures the protection of systems against all unauthorized access (IAM). In addition to protecting the hardware, there should be more control placed on software, processes, and people. Another critical point on security is change management.
In our fast-moving world, people change their roles frequently. When a new CIO takes control, will there be vulnerabilities at the time of transition? You should address both physical and logical issues.
Finally, how does an organization mitigate risks? Are there effective systems to help recover fast from a disaster? Because security is a common principle across several cybersecurity protocols, companies that adhere to this protocol can easily implement other principles.
Principle 2 — Availability:
Availability is a contract between the company and the buyer. What products and services are available for use? Do customers understand their limits? If they don’t agree to the limits, companies are more likely to be victims of phishing tactics. The principle of availability requires all products and services to be available at the right time. The customer should understand the guaranteed uptime percentage, downtimes, and time for maintenance. And, of course, ensure products and services are of the right quality. You can implement this principle using a Service Legal Agreement (SLA).
Principle 3 — Confidentiality:
When giving access to systems and applications, are you confident with the user? If a third-party vendor visits to assist in your cloud migration, are you confident the vendor has the right skills and professionalism to conduct the process? Instead of relying on plain old intuition, use available technology to increase confidence. Technologies, such as encryption, cryptography, and firewalls, can help keep data confidential. It’s all about confining information and processes within a manageable network.
Principle 4 — Processing Integrity:
The principle applies to eCommerce — any transaction that happens online. If you process frequent transactions, then there’s a high risk of being a target. Services and products offered online should have authorization. Even blunt products, such as knives and hunting tools, have to meet strict criteria before anyone can sell them online. Make sure every transaction is authentic. Inauthentic transactions can lead to chargebacks, lawsuits, and even damage to your reputation.
Principle 5 — Privacy:
Privacy varies from one industry to another. There’s physical privacy where we protect what we see and listen to. And there’s IT privacy that ensures our systems don’t exfiltrate sensitive information. The privacy principle ensures you collect and acceptably use consumers’ data. The most common information includes names, phone numbers, and e-mail addresses. Before sending a marketing promotion or sharing this data with your partners, you must get the user’s consent. This must be real consent, not just through technical terms and conditions where everyone scrolls through like lightning.
Just obtain the data you need and, if possible, have a disclosure. There are several steps and executions needed to stay compliant. Implementing all recommendations can be confusing. But with the right advice, even small businesses can implement the five trust principles. If you need help starting, contact us here https://nops.io/.