- Blog
- Cost Allocation & Reporting
- How I Saved My Company $15,000 by Finding and Removing Untagged AWS Resources Using nOps Cloud Management Platform
How I Saved My Company $15,000 by Finding and Removing Untagged AWS Resources Using nOps Cloud Management Platform
I’ve been thinking about how to start this post for the past week. Do I start it off with “Why does every Cost Optimization webinar, conversation, or chat always talk about tagging or the lack thereof?”
Probably for the same reason that I’m writing this post about tagging and how I saved my company $15k in untagged resources.
Here’s how the typical engineer or person about to deploy something new on AWS rationalizes not using tagging.
Honestly, what’s the big deal if I’m going to test out a New Amazon EC2 instance and I don’t tag it? I plan to terminate it immediately as soon as I’m done testing it out at the end of the day.
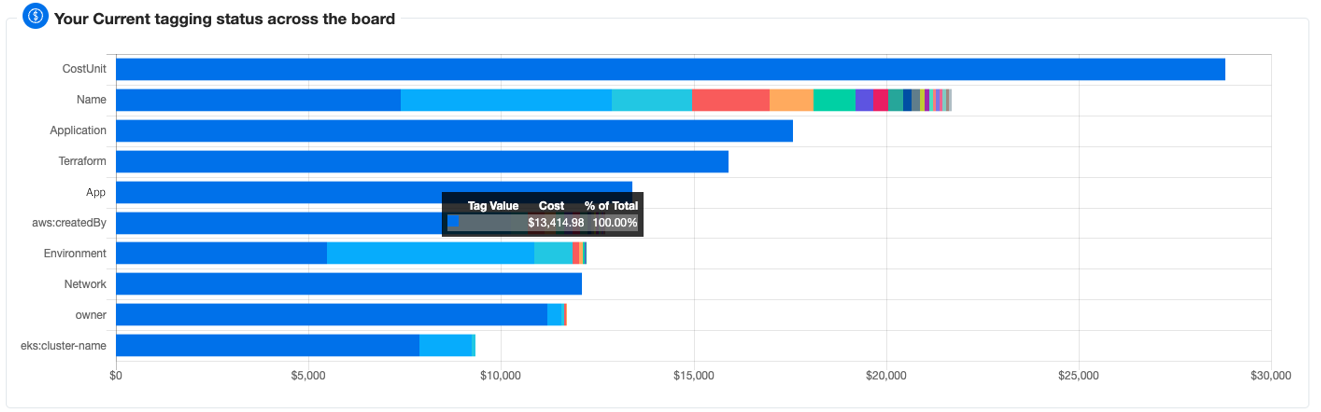
But here’s what really happens. They get sidetracked and forget to terminate the instance or delete the resource at the end of the day. That day becomes two, three days, weeks, months. Then six months later while performing a routine cost optimization effort using nOps Tag Explorer for Cost Control, you start to ask yourself, “How are untagged resources our 5th most expensive cost in AWS?” Surely all my stuff is tagged but at the same time, not all AWS Resources support tags.
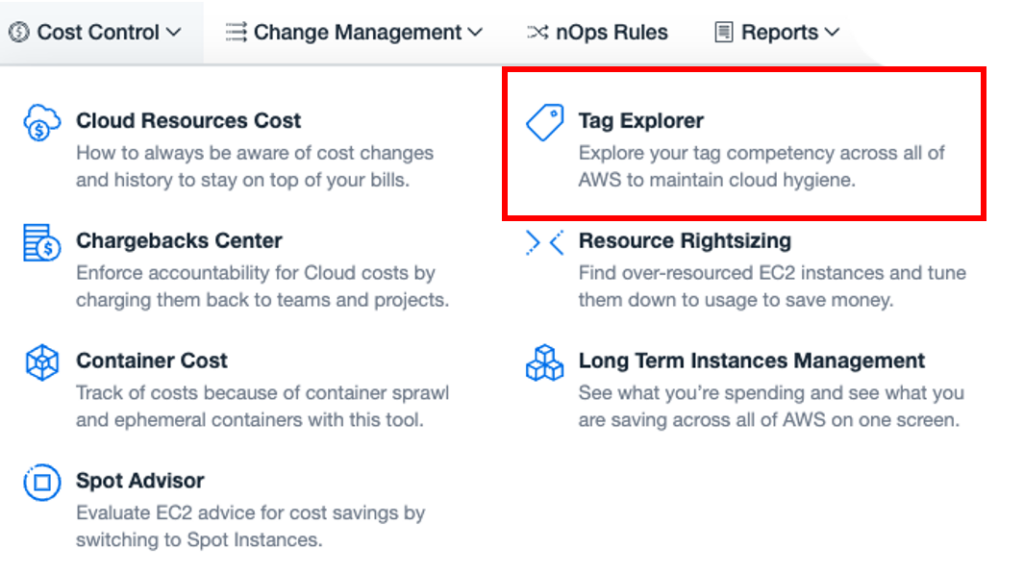
Find Untagged AWS Services Using nOps Tag Explorer
Now, I bet you’re wondering how the heck I saved nOps $15k and how does tagging have anything to do with it? What if I told you that while we were going through a demo of nOps, I focused on the top four Untagged AWS Services using the nOps Tag Explorer for a detailed view and breakdown.
The first part of this post is to walk through and identify the Top Four items that are costing us the most in the last 30 days. Yes, the default view is 30 days, imagine if we showed the cost for six months or a year!
I started to drill into the list of resources that were untagged.
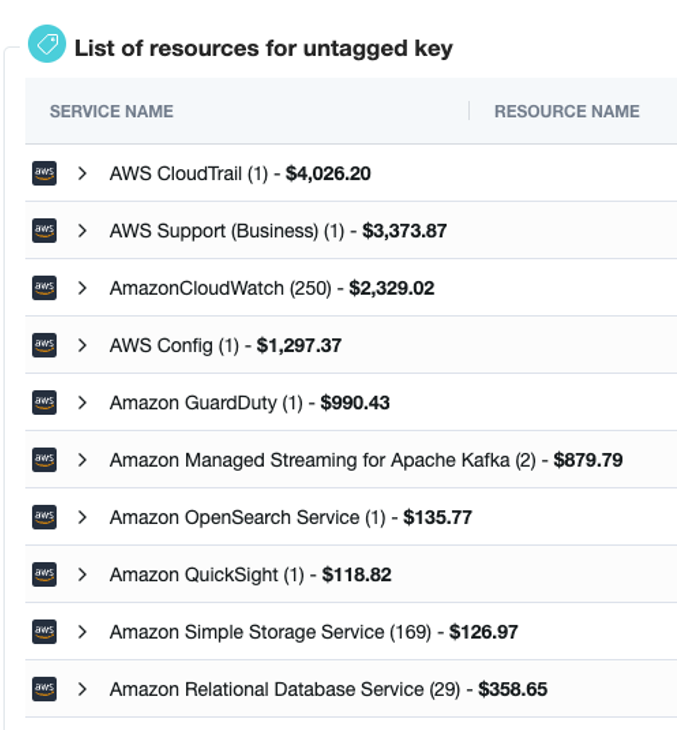
Untagged #1: AWS CloudTrail.
Does it seem worthwhile to tag AWS CloudTrails? If you aren’t familiar with AWS CloudTrail, think of it as a record of all the events that happen within your AWS Account(s). You could have multiple CloudTrails per account used for different purposes, maybe one for Security access only or Auditing. Since CloudTrail supports tagging why not tag the trail to identify what it is being used for or who’s using it. In the last 30 days, we’ve spent $4,000 on CloudTrail logs, which seems really high.
Untagged #2: AWS Support
AWS Support plans currently do not support tagging but are a non-resource-specific cost. It would be nice if we could tag each AWS Support Plan(s) to note or allocate the cost to a certain account for chargeback/show-back purposes. Maybe this is a feature request I need to submit, excuse me, I’ll be right back.
Untagged #3: Amazon CloudWatch
Why am I not surprised that Amazon CloudWatch is up there with our most costly AWS Service? This is another AWS Service that does not support tagging, but you can provide a descriptive Alarm Name and details within the description to understand the usage or requirement. I just wish that we could tag each alarm for billing and searchability. Amazon CloudWatch is used to monitor your AWS resources and application in real-time and in this case, we have 250 Amazon CloudWatch metrics without tags. Costing us over $2,300 for the last 30 days.
Untagged #4: AWS Config
Let’s look at the last item for today, AWS Config. AWS Config is used to assess, audit, and evaluate the configurations of your AWS resources continuously. For the last 30 days within our single AWS account, we’ve spent $1,300 (and since it takes me a little bit to write a post, we are now over $1500). Costing us approximately $8,000 for the next 6 months

Since AWS Config is a non-resource-specific cost, you’re billed on the number of configuration items recorded. But that doesn’t mean we can’t tag each of the Rules being used. Unfortunately, for every resource or service that can be tagged within the AWS Console, Tagging is completely optional.
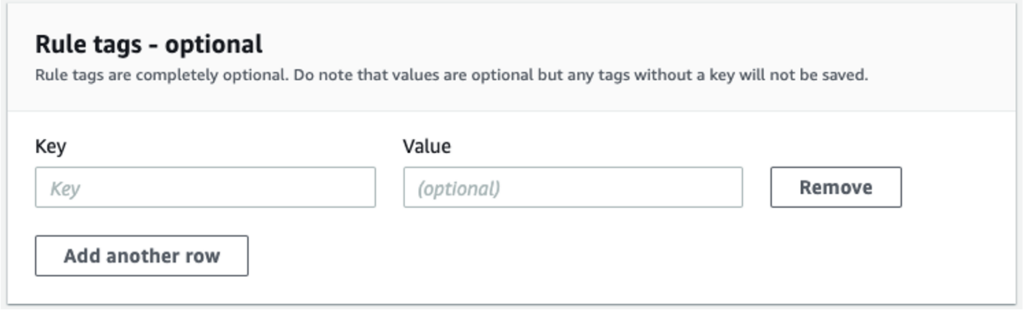
Now I know you’re thinking, how can something so important to billing, automation, and accountability be optional? Unless you are enforcing tagging or terminating any services that aren’t properly tagged, no one is going to do it.
AWS Cloud Cost Allocation: The Complete Guide

Actions
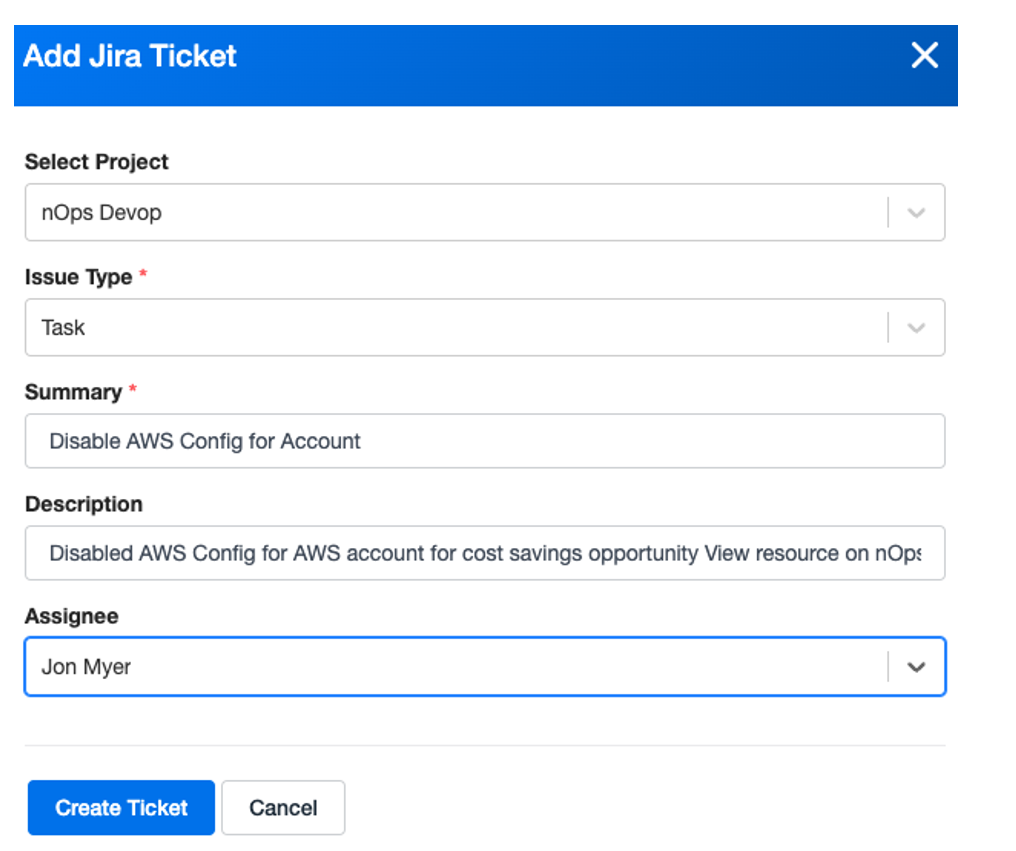
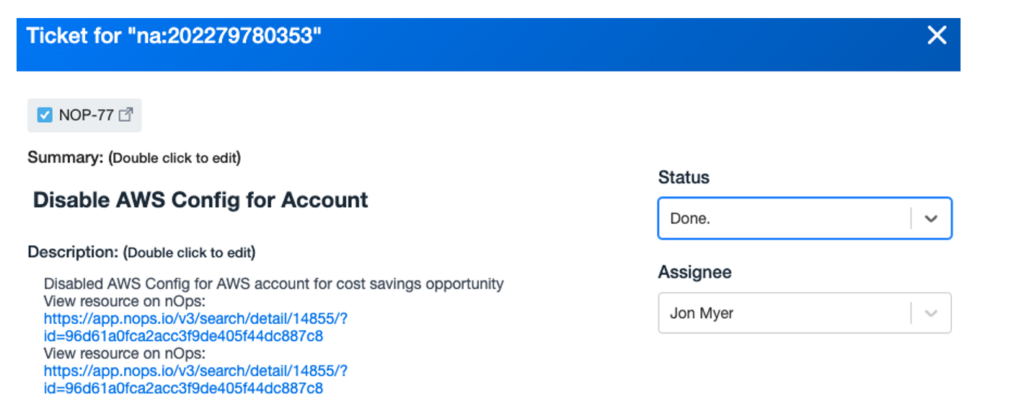
Here’s where I start to open JIRA tickets for the Top Four Untagged Services using nOps JIRA integration feature. Forcing each of the teams to go back and review their tagging strategy, and remove/delete unused AWS Services and resources. The alternative is, that I’ll happily terminate or delete any AWS Service or Resource that can be tagged but missing tagging information.
After forcing the teams to tag or untagged resources that are not being utilized. Here are the results.
AWS CloudTrail
We have a total of five trails, two of them are enabled and already have tagging, plus one for the engineering team. After removing the three unused, untagged, and disabled trails, we’ve saved nOps $6,000 over the course of the remaining year.
AWS Support Business
Unfortunately, we need the support and at the same time, we can’t tag support so this is an item that will always show up on the Tag Explorer console.
Amazon CloudWatch
I wonder how many companies clean up their Amazon CloudWatch alarms. In all honesty, I don’t think I’ve ever deleted a CloudWatch Alarm within a testing environment unless it was deployed using Amazon CloudFormation. After looking at the number of alarms configured and trying to determine which ones weren’t being used. I was able to clean up some, but further investigation was required. Which meant, time to open a few more JIRA tickets. I’ve estimated that I was able to clean up a few but Amazon CloudWatch doesn’t cost too much and probably saved around $1000 for the year.
AWS Config
AWS Config was the fourth highest item on my Untagged resource list. After opening a JIRA ticket to our engineering team, it looks like AWS Config was enabled for testing but wasn’t turned off, costing us $1,300 a month. At the same time, we don’t know who turned it on and what type of testing was being done. This means, that by turning it off, we could cause issues on our backend R&D but our company policy requires everyone to tag AWS Resources and Services.
By disabling the Recording, we could still access the current records since they are stored in an Amazon S3 bucket. We could take this one step further and delete the S3 bucket to save additional cost or convert the bucket to a cheaper storage class like infrequently accesses or Amazon Glacier. Maybe that’s a future post or article. In total, we saved approximately $8,000 by disabling this service.
The total cost that we saved by reviewing all our untagged resources easily within the nOps console for the year is $15,000. Imagine performing this exercise monthly utilizing the cost visibility within nOps or enabling our future automation feature for tagging resources directly from the nOps Console.
Are you looking to give nOps a try? Check out our Free Trial offer to get started on using our data-driven cloud management platform to help streamline and automate your operations while lower cloud costs and reducing compliance risks.

Jon Myer
Chief Evangelist
nops.io
Jon Myer is a technical content creator, that told his kids “you’ll never find me on YouTube”. Never say never. He’s a technical storyteller, and before joining nOps, a self-proclaimed evangelist, who inspires others to share their story because everyone has a story to tell. He brings his passion for sharing content through videos that allow him to be quirky, engaging, and entertaining all while bringing informative content.
Related Topics
Avoiding Bill Shock — How to Detect and Mitigate AWS Cost Anomalies