- Blog
- AWS Compliance
- Best AWS Security Compliance Practices
Best AWS Security Compliance Practices
The AWS cloud environment is rapidly changing, and all assets require robust security. A secure cloud environment not only improves a business’ reputation but also elevates the customer experience.
AWS by itself is secure, but you have to play a part in maintaining high security levels. This is because security is a shared responsibility between AWS and the customer. While AWS is responsible for securing the cloud architecture, it’s your responsibility to ensure all workloads are secure from risks and threats.
Organizations that operate in sensitive environments, such as finance, health care, education, mortgage, etc., have to stay compliant with the various regulatory standards.
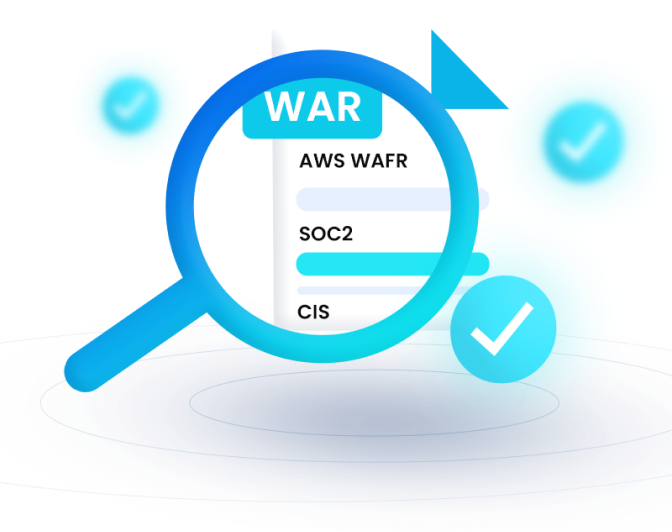
Here, we highlight some AWS security compliance practices that ensure you comply with standards, such as PCI, ISO 27001, HIPAA, and more.
1. Map Your IT Assets
Identifying the key IT assets is the first step toward AWS security compliance. It’s impossible to secure assets that you are not aware of.
First, identify all assets you need to secure, from applications, code, data, and servers. With all assets in the picture, you can devise a way to secure them from threats, both external and internal.
Organize assets into categories in terms of priority. This allows you to know what you need to safeguard your business.
2. Implement an Information Security Management System (ISMS)
An Information Security Management System (ISMS) is an IT asset management system defined by the ISO 27001 standard. It allows you to set the processes to perform crucial IT tasks, such as:
- Analyzing and evaluating business impact in the event of risk occurrence.
- Identifying risks to IT assets.
- Defining data control techniques and security policies, rules, and objectives.
- Selecting risk management strategies.
3. Set Up AWS Identity and Access Management
The majority of regulatory standards require proper identity and access management protocols. If AWS hosts your IT assets, you can use the AWS Identity and Access Management (IAM) feature to manage who can access specific resources.
The IAM allows you to manage AWS resources’ permissions. With the IAM, you can create users and groups and assign roles. This ensures users can access AWS resources that they have permission for.
4. Secure Data at Rest
When you have buckets that you no longer access or belong to past workloads, you can delete them entirely. All you need is to enable the activity metrics that help discover dormant buckets. Once you have discovered the dormant buckets, you can decide whether they are worth keeping or deleting.
5. Monitor AWS Accounts for Abnormalities
With sophisticated attacks and targeted threats, a security mindset is never enough to safeguard workloads. It’s best to implement real-time monitoring and threat detection to secure your crucial IT assets.
Host monitoring and intrusion detection help you discover anomalies in your AWS environment. With these strategies in place, you can quickly analyze applications seamlessly. Also, you can monitor user behavior in workloads, such as data transfers, machine communication, access control changes, and much more.
Conclusion
AWS security compliance practices are essential for a variety of reasons. It allows you to stay in line with compliance requirements and helps protect crucial data. Implementing the above practices will safeguard crucial business data and prevent the disruption of crucial business processes.
At nOps, we help organizations implement the best AWS security compliance practices to protect IT assets. The nOps security and compliance tool allows for continuous monitoring and tracking of user behavior. You can detect threats and risks in real time. It also provides detailed audits trails of security breaches and ensures you are compliant with industry standards.
Looking for more security and compliance help? Check out the AWS Guide to Security and Compliance.
Last Updated: February 1, 2024, AWS Compliance
Last Updated: February 1, 2024, AWS Compliance