- Blog
- AWS Compliance
- How to Achieve AWS Compliance
How to Achieve AWS Compliance
Last Updated: February 1, 2024, AWS Compliance
As organizations continue to adopt cloud computing, data security and regulatory compliance remain mandatory. Securing your cloud resources is a big step forward towards achieving compliance. Being compliant empowers the organization to operate within an AWS security control environment.
AWS (Amazon Web Services) compliance means achieving all regulatory requirements for standards that your business has to meet when deploying resources in AWS. It’s a set of procedures and solutions that AWS customers leverage to achieve compliance.
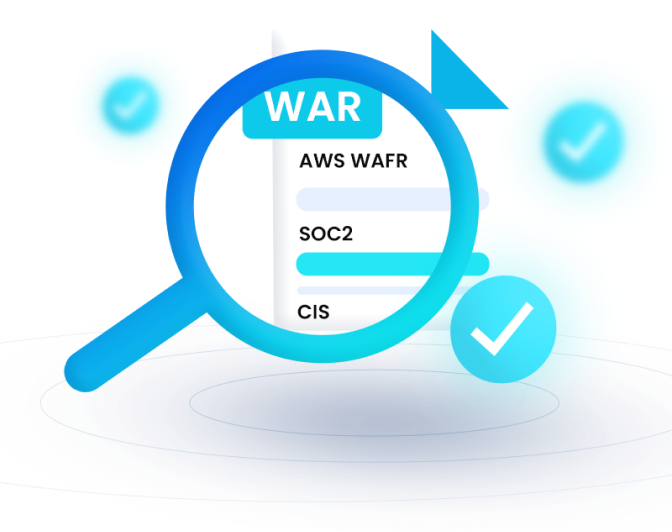
AWS is an on-demand, compliant-ready cloud computing platform for some regulations such as PCI (Payment Card Industry) DSS (Decision Support System) and SOC2(Service Organization Control). However, you need to play an essential part in maintaining overall compliance. Compliance in AWS is a shared responsibility, meaning AWS is responsible for compliance with regulations that apply to the infrastructure. As an AWS customer, you are responsible for regulations that apply to stored data, applications, and service usage.
Also Read: What Is Amazon Web Services (AWS) Compliance?
Six of the Best Ways to Achieve AWS Compliance
AWS compliance is a continuous process, meaning you have to stay on it at all times. Here are some of the best ways to achieve compliance for the various regulatory standards you may face:
Real-Time Monitoring
To be AWS compliant, you have to keep monitoring your resources at all times. Thankfully, there are lots of tools, both AWS-native and third party, that you can leverage to ensure 24x7x365 monitoring. Amazon CloudWatch and CloudTrail come in handy to give you 360-degree visibility into your cloud environment. You can also use third-party monitoring tools such as nOps and VMWare to monitor all activities in your cloud environment.
With real-time monitoring, you stay updated at all times. You can rely on real-time alerts to identify and remediate anomalies in your cloud.
Identity and Access Management
All regulatory standards require organizations to control who can access data stored in their systems. Therefore, you need to provision your AWS Identity and Access Management feature to ensure only allowed users can access crucial data.
Some of the top Identity and Access Management strategies include:
- Multi-factor authentication
- Password policy
- Least privilege access
- Using customer-managed policies
- Rotating access credentials regularly
- Using roles to delegate permissions
During regulatory audits, auditors will check most of these items often. Therefore, it’s best to ensure you meet all of the above.
Proper Cloud Configuration
Most of the data breaches in the cloud occur due to misconfigurations. How you configure your cloud resources determines whether they are secure or not.
Cloud misconfigurations are any gaps, errors, or glitches that expose your resources to cyber threats. It can be wrongly set security groups, un-encrypted data, lack of multi-factor authentication, and more.
You should proactively find and fix any misconfigurations with automated remediation. Scanning your AWS environments at set intervals helps detect aspects of the cloud that are misconfigured.
Always Encrypt Data
Most regulatory standards require organizations to encrypt data at all times. Encrypting data in transit and at rest makes it unusable unless decrypted. In this case, a malicious attacker cannot compromise data without a decryption key. Encryption makes data unreadable so that no human or machine can comprehend the contents of the data.
You can use SSL/TLS (Secure Sockets Layer/ Transport Layer Security) standards with strong policies for data encryption. You can also use AES-256 encryption to encrypt data with ease.
Collect Security Events and Audit Logs
Regulatory requirements dictate that organizations implement audit logging. Audit logs help identify and detect security issues and any anomalies from malicious activity. You should always collect security events, logs from cloud services and applications and store them for a certain period as per the requirements.
Your organization should collect RDS (Radio Data System) access logs, EC2 (Elastic Compute Cloud) logs, and S3 (Simple Storage Service) logs. You should collect and review logs such as intrusion detection and vulnerability scanning frequently. Services such as AWS CloudTrail and CloudWatch help with compliance audit logging.
Always Back Up Crucial Data
Every organization that operates in a sensitive environment should have a data backup and disaster recovery plan. To avoid losing data, you should have backups and a strategy to recover that data in case of loss.
Amazon provides the S3 Glacier and Glacier Access storage tiers specifically for backup data. Therefore, you can always set data backup at specific intervals and configure a recovery procedure. On top of backup, you can add encryption as an additional layer.
Remember, most regulatory requirements like HIPAA (Health Insurance Portability and Accountability Act), SOC2 (System and Organization Controls), and others require organizations to have disaster recovery and data backup.
Achieve AWS Compliance With nOps
Unlike other cloud platforms, nOps helps users achieve compliance quickly. You can use the available services to monitor the cloud environment, secure data, and collect logs.
At nOps, we enable users to achieve HIPAA and SOC2 compliance. nOps provides visibility into your entire cloud environment, allowing you to detect anomalies, remediate issues faster, configure their cloud, and achieve compliance easily.
Start your nOps free trial today, or schedule a demo to see it live in action!