- Blog
- Cost Allocation & Reporting
- nOps Rules – Tag Violation
nOps Rules – Tag Violation
Monitoring for tag compliance is the most effective way to ensure compliance for your cloud environments. If your organization doesn’t enforce proper tagging policies, eventually, no one will know who originally launched the resources and for what purpose.
With nOps’ flexible tag-violation configuration, you will receive real-time notification if newly launched resources violate the tag policy. Let’s say if someone launches an instance with no Name tag, or if the value is empty or value doesn’t contain certain string, you’ll get real time notification with the context about who launched the resource. This is win-win situation, engineers can still experiment fast and IT can trace back every single resource.
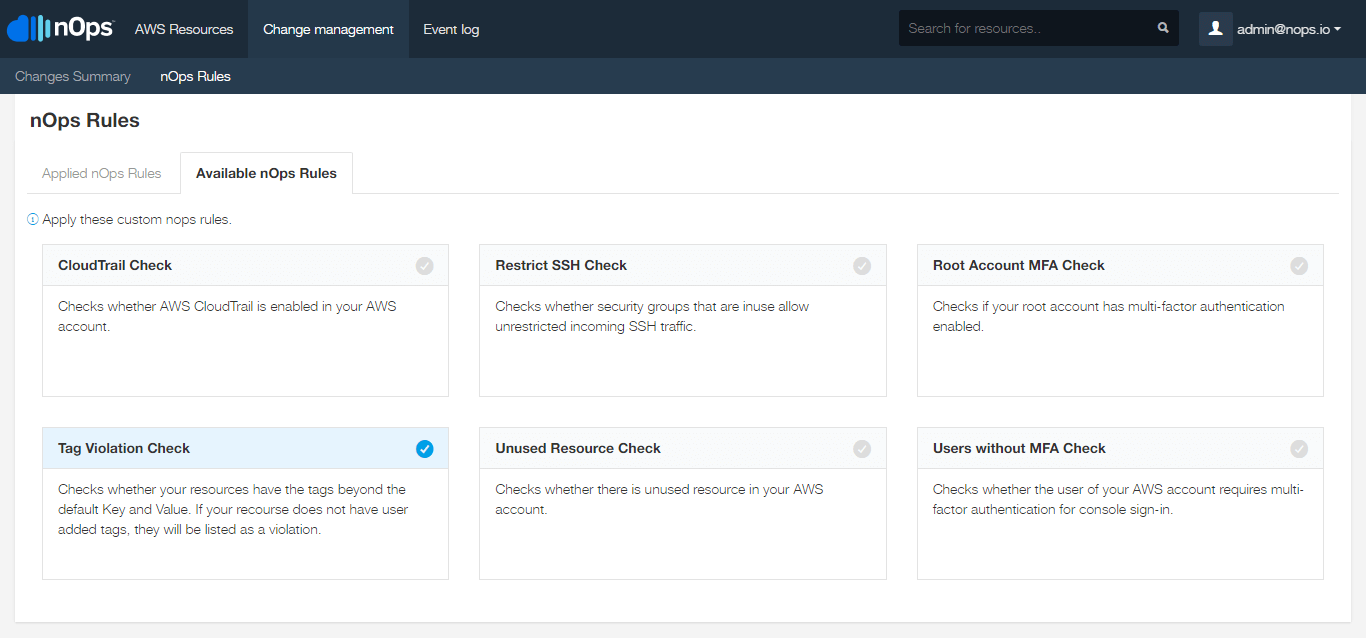
Tag Violation Rule
To enable the rule, simply go to the “Available nOps Rules” tab in nOps Rules and click on the “Tag Violation Check” rule.
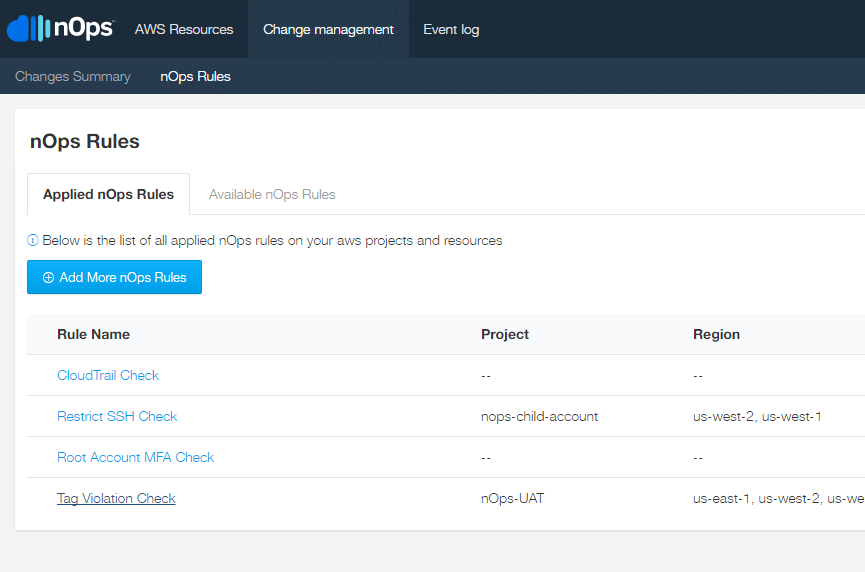
Tag Violation Summary
Once enabled, the rule will appear on the “Applied nOps Rules” tab with a summary of all resources that violates the rule.
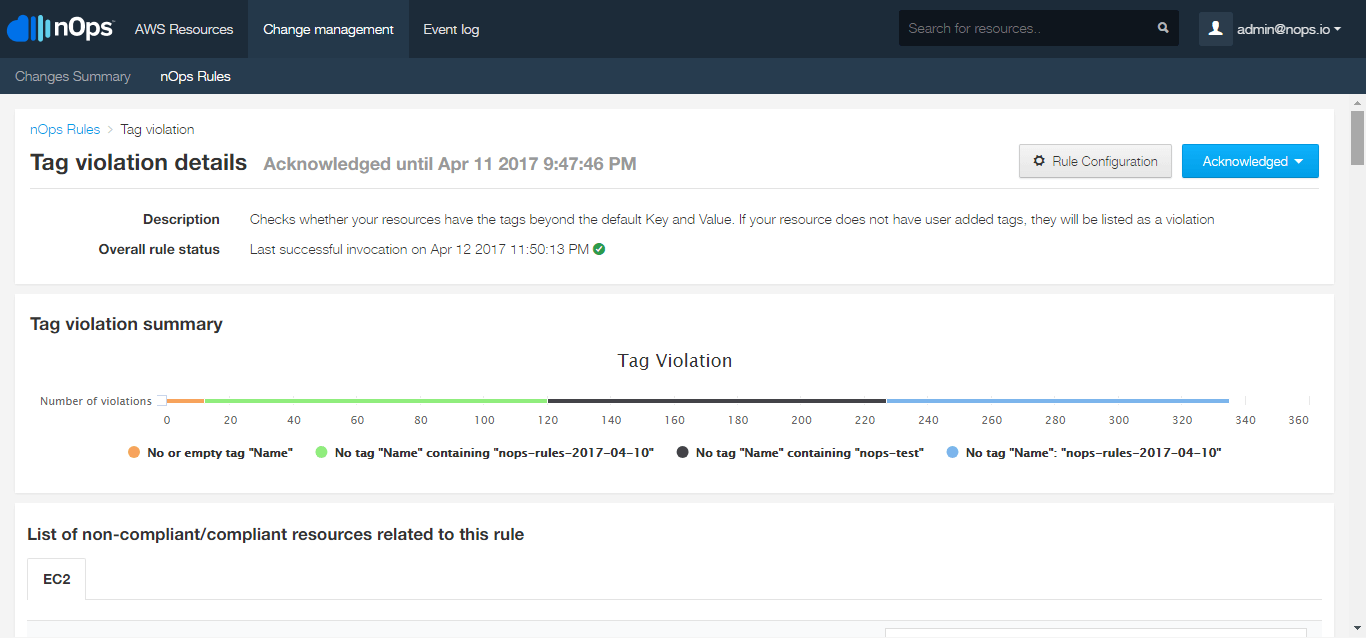
Tag Violation Detail
Clicking on the rule in the “Applied nOps Rules” tab, you will be able to see, in detail, the number of resources and for which tag configurations do these violations occur.
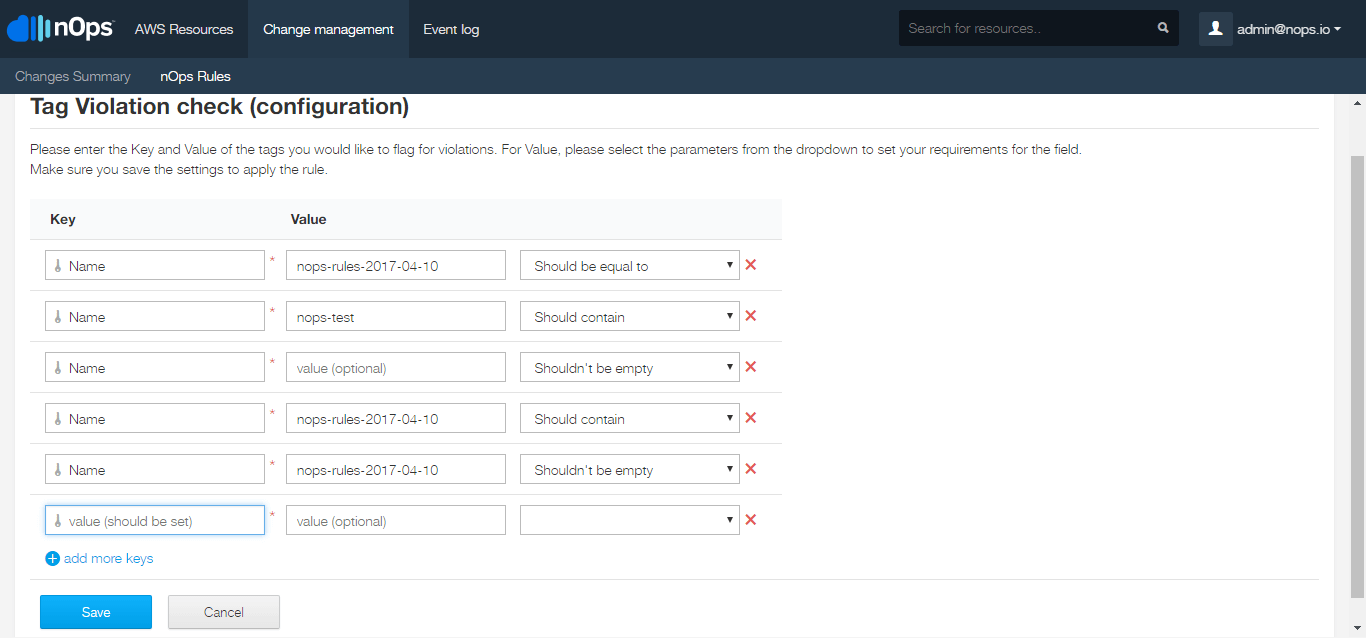
Tag Configuration
To customize this rule to fit the unique nomenclature of your tags, if you use them, you can configure the tags in the Rule Configuration page.
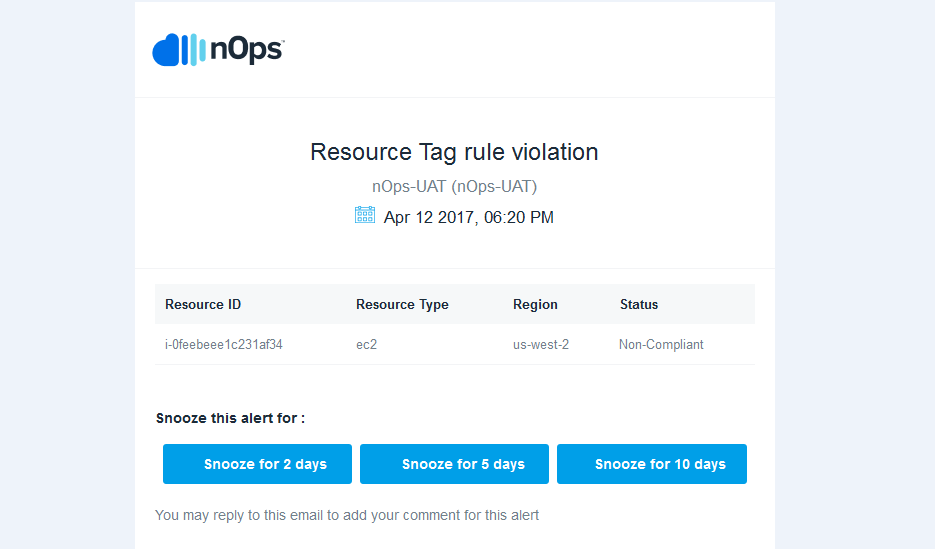
Tag Violation Alerts
Once enabled, you can configure your nOps account to receive email, Slack, and/or Hipchat alerts, alerting you to newly recreated resources that violates the rule.