- Blog
- AWS Compliance
- Using the AWS Well-Architected Framework to Support DevSecOps
Using the AWS Well-Architected Framework to Support DevSecOps
Last Updated: February 1, 2024, AWS Compliance
Achieving speed and reliability in product delivery is the essence of DevOps, but it’s critical not to compromise security in the process. Instead of considering security measures at the end of the delivery lifecycle, a DevSecOps approach integrates security throughout the product delivery lifecycle. This is often referred to as “shift left” – moving security earlier in the process.
DevSecOps blends the lean principles of agile with delivery speed and secure code.
DevSecOps is gaining traction. A 2017 Gartner report projects that, by 2021, DevSecOps practices will be embedded in 80% of rapid development teams, up from just 15% in 2017.1
In this first in a series of blog posts, we’ll share some strategies for applying guidelines from the AWS Well-Architected Framework in a low-friction way to make it easier to prioritize security and advance your DevSecOps approach.
If you’re not familiar with the AWS Well-Architected Framework, it’s a set of best practices developed by AWS solutions architects to help cloud architects build secure, high-performing, resilient, and efficient infrastructure for their applications. It’s based on five pillars — operational excellence, security, reliability, performance efficiency, and cost optimization.
Security Pillar of the AWS Well-Architected Framework
In the security pillar of the Framework, information, systems, and assets are protected, while business value is delivered through risk assessments and mitigation strategies. This pillar defines security in the cloud by the following five components:
- Identity and access management
- Infrastructure protection
- Data protection
- Detective controls
- Incident response
So, how can you easily apply Well-Architected Framework guidelines to strengthen the Sec in your DevSecOps? You need to have processes in place, built on the principles above, to ensure alignment and implementation of best practices.
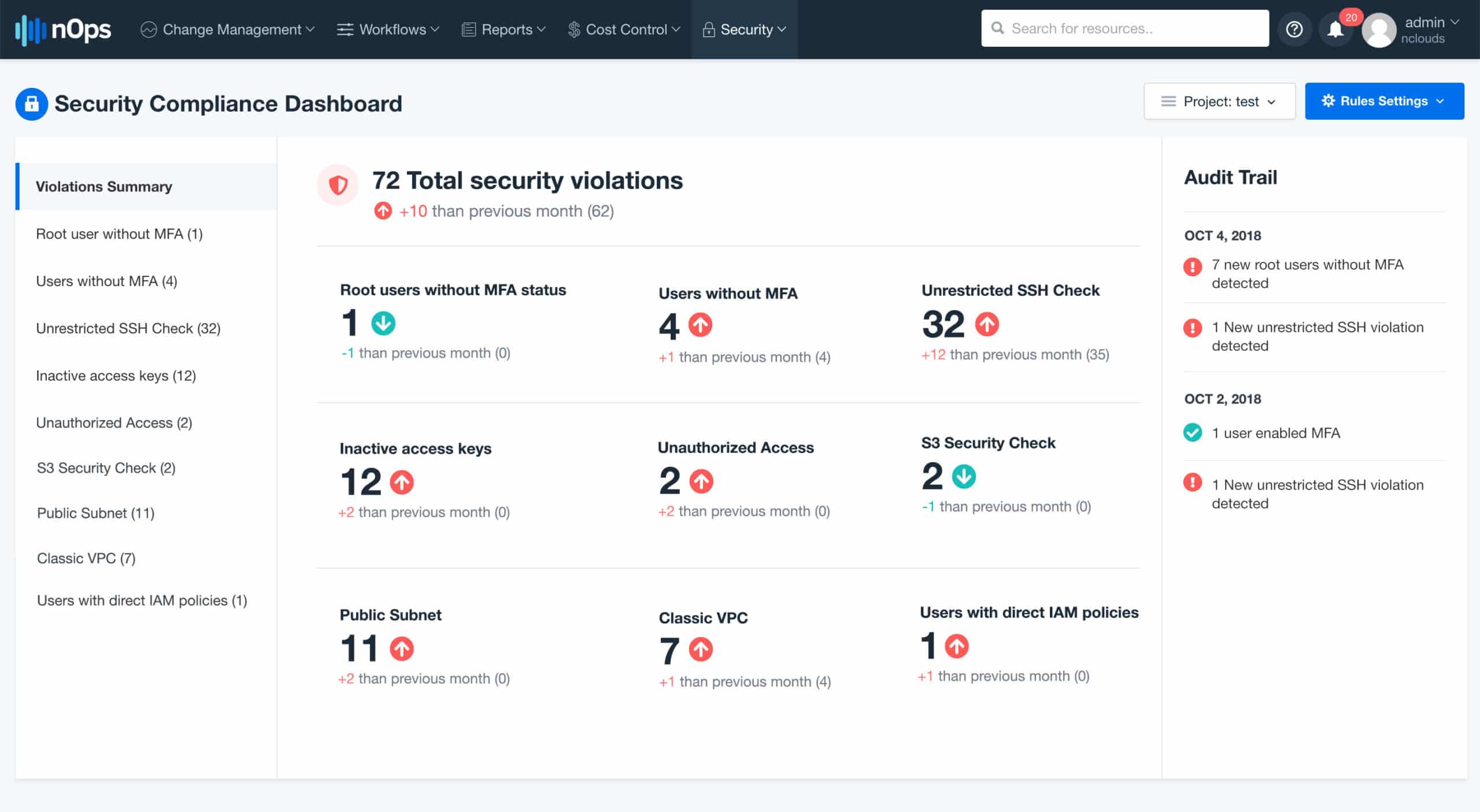
nOps cloud management for AWS is an easy-to-use SaaS tool that enables DevOps teams to create customized security profiles to identify and support remediation of security violations aligned with AWS Well-Architected Framework guidance. It includes predefined rules to help you avoid security breaches and achieve compliance with industry standards. Plus, you can create your own workload and configure it within nOps.
The following are key tactics and considerations aligned with the five components of cloud security from the AWS Well-Architected Framework security pillar. I’ve indicated where nOps offers pre-defined rules associated with these tactics.
| Security Components of AWS Well-Architected Framework | Tactics & Considerations |
|---|---|
| 1. Identity and access management (IAM) |
|
| 2. Infrastructure protection |
|
| 3. Data protection |
|
| 4. Detective controls |
|
| 5. Incident response |
|
Enable root MFA
You must protect your root account with multi-factor authentication (MFA), even if you don’t root the account often. Companies like Netflix install physical MFA for the root and lock up the key. What happens when root MFA is disabled? Not to worry – nOps checks root account usage patterns that can create security risks, and it provides you with immediate alerts. You can secure multiple accounts with nOps. We also recommend that you use AWS Organizations – you can avoid having a root account for each account, additional accounts to an organization, and simply manage a single root account. We’ll explore this more in an upcoming blog post.
User without MFA
You can force MFA with an external identity provider like Okta. However, if you don’t have that in place, how do you identify users without MFA, requiring remediation? nOps ensures that all user accounts are MFA-enabled, and it provides you with details on accounts that are not MFA-enabled so that you can remediate easily.
Implement a strong identity foundation
The next step is to make sure you create a model based on the principle of least privilege (PoLP). Attach fine-grained policies based on teams. Many companies use Okta SSO or Amazon SSO. How can nOps help? By providing real-time monitoring and notifications based on policies attached directly to the user rather than creating roles.
Don’t use access keys
If you take away only one thought from this blog post, remember this: Don’t use access keys, particularly for your AWS account root user. If you read the headlines about company after company getting hacked, it’s often because a hacker compromised the key. In lieu of long-term access keys, use temporary security credentials (IAM roles). If you do need to create access keys for programmatic access to AWS, create an IAM user, grant that user only the permissions they need and generate an access key for that user. In such a case, be sure to watch out for inactive keys. With nOps, keys are monitored and you’ll get real-time alerts on those that are inactive so that you can remove them.
Incident detection and response
Instead of taking a reactive approach to incident response, it is easier, faster, cheaper, and more effective to detect, react, and recover proactively. With automated detection, behavioral-based rules are used to identify and detect breaches or spills. nOps applies a rule for AWS CloudTrail monitoring. Another nOps rule makes sure there is tagging to identify resources and find owners and administrators, to facilitate incident response. Changes to your environment are the start of most incidents. nOps’ powerful change management features help to pinpoint the exact change and associate it with the incident in order to take corrective actions.
Supporting DevSecOps with AWS Service Catalog and nOps
AWS Service Catalog provides another strategy for advancing your DevSecOps initiative. DevOps teams can use Service Catalog with the nOps workflow engine to control and accelerate cloud deployment while adhering to organizational security measures seamlessly and consistently. You can empower teams to speed service delivery by creating standard services that can be integrated with custom workflows. And, make teams productive and compliant by providing secure access to reusable, standard services when it’s not viable for all team members to have access to AWS or compliant environments like HIPAA/HITRUST, for example. Learn more about workflow automation and AWS Service Catalog.
The AWS Well-Architected Framework provides invaluable guidance for creating cloud infrastructure that is secure, high-performing, resilient, and efficient. With nOps, we’re making the Framework actionable – easy to implement and achieve continuous compliance with essential guidelines.
Watch the video
JT Giri provides highlights from his AWS re:Invent 2018 presentation, “Get Well-Architected for Continuous Compliance and DevSecOps.” Learn how DevOps teams use nOps to support automated discovery and continuous compliance as part of building a well-architected infrastructure on AWS and advancing their DevSecOps initiative.
Learn more about nOps cloud management for AWS
Check out nOps’ security & compliance features. Plus, learn how nOps supports the AWS Well-Architected Framework for cost optimization, too.
www.nOps.io
Endnote
1. MacDonald, N. and Head, I. (2017). 10 Things to Get Right for Successful DevSecOps. [online] Emtemp.gcom.cloud. Available at: https://emtemp.gcom.cloud/ngw/eventassets/en/conferences/lsc37/documents/gartner-io-cloud-us-research-note-successful-devsecops-2018.pdf [Accessed 18 Nov. 2018].