- Blog
- AWS Compliance
- Factors to Consider When Choosing an AWS Security & Compliance Tool
Factors to Consider When Choosing an AWS Security & Compliance Tool
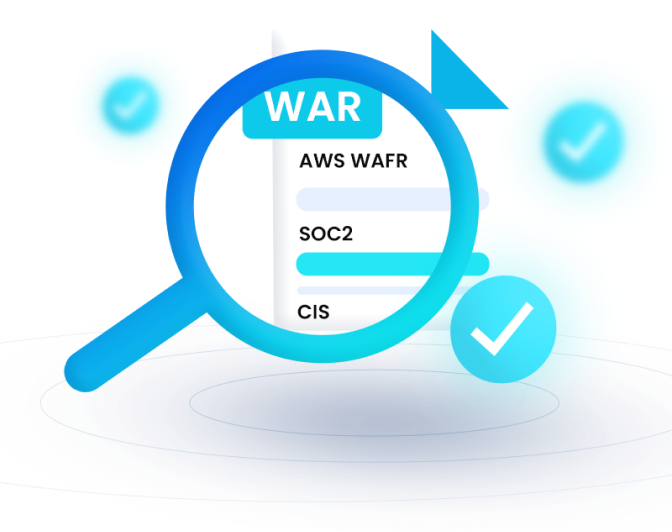
Organizations that handle crucial customer data and personal information have to comply with various regulatory requirements. Some of the most common regulatory standards include: The General Data Protection Policy (GDPR), Service Organization Control (SOC 2), Health Insurance Portability and Accountability Act (HIPAA), Center for Internet Security (CIS) Information Security Operations (ISO 27001), and National Institute of Standards and Technology (NIST 800 171).
Being compliant for the numerous regulatory can be a challenging prospect. Failure to comply can lead to loss of certification, which may ruin your organization’s reputation and hinder business operations. Having an AWS security and compliance tool can help you stay in line with the various regulatory requirements. However, choosing the right tool can be difficult, as there are tons of products available in the market.
Here are the factors you should consider when choosing an AWS security and compliance tool:
Security Alerts and Notifications
Most compliance standards require security alerts to keep you updated on all security instances. A security alert can help you respond to emergencies on time and control damages before impacting the more extensive network in an organization.
The ideal AWS (Amazon Web Services) security and compliance tool should also have good uptime and a backup plan if the primary notification system fails, which is also known as secondary protection. For instance, you can choose a tool that packs various alerting features, including messages, email, and geo-tagging technology for alerts. Some of the alerts include:
- Anomalous behavior in cloud usage
- An unexpected surge in cloud bill
- An alert about user credentials found in a data breach
- A notification about malicious login attempts and many more
Identity and Access Management
A good AWS security tool should help you implement the basics of identity and access management. One essential feature is limiting access to unauthorized users. Other identity and access control features include:
- Data encryption features to protect the cloud infrastructure
- Limiting remote access to the cloud environment, based on working hours, location, and other factors
- The ability to terminate idle sessions
Finally, the AWS compliance tool should help beginners set strong but memorable passwords and remind users to change passwords occasionally.
Real-Time Monitoring Dashboards
Unlike basic notifications, real-time monitoring is more effective in understanding cloud operations. Real-time monitoring allows you to identify and detect threats and vulnerabilities in your systems. Modern malicious attacks are persistent, and weaken each security layer. In such cases, you cannot rely on typical notifications alone. A real-time monitoring tool that logs actions in real-time can help you protect customer data and stay in line with compliance.
Pre-Defined Security Rules
Pre-defined security rules should help in responding to certain situations. Like automation, these rules should help you know what to do in difficult circumstances. Your security and compliance tool should have prebuilt and customizable security rules to provide automated alerts and checks.
Cloud Infrastructure Health Scan
After implementing most security practices, perform a detailed health scan. Most regulatory requirements require frequent security scans, as they help detect weaknesses and potential vulnerabilities.
A cloud security health scan will give an estimate of where you are in the compliance process. In addition, great AWS security tools offer positive recommendations after each scan. Implementing the recommendations in the cloud health report increases the chances of being compliant.
Conclusion
The above features are highly essential to consider when choosing an AWS security and compliance tool. With a tool that offers the above capabilities, it’s easier to stay compliant.
nOps helps you to check your cloud environment against the AWS Well-Architected best practices to help you stay in line with compliance. It helps you perform cloud health scans, monitor logs, and more.
Start your nOps free trial today, or schedule a demo to get started!
Last Updated: February 1, 2024, AWS Compliance
Last Updated: February 1, 2024, AWS Compliance